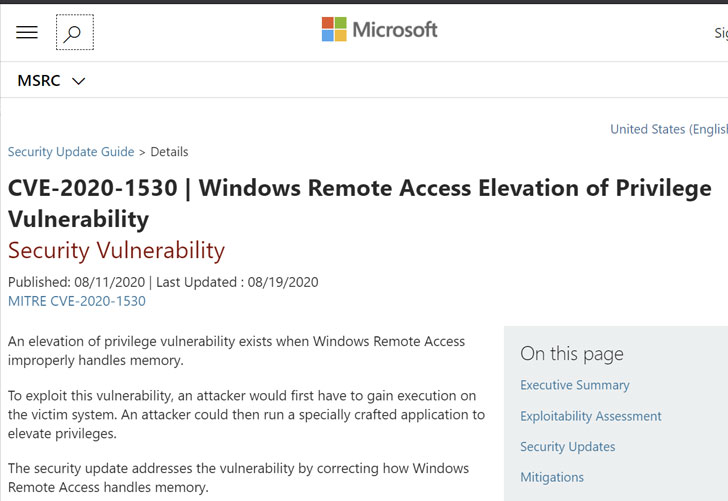
Microsoft Releases August Security Release for Windows PCs, Fixing 93 Vulnerabilities | Technology News
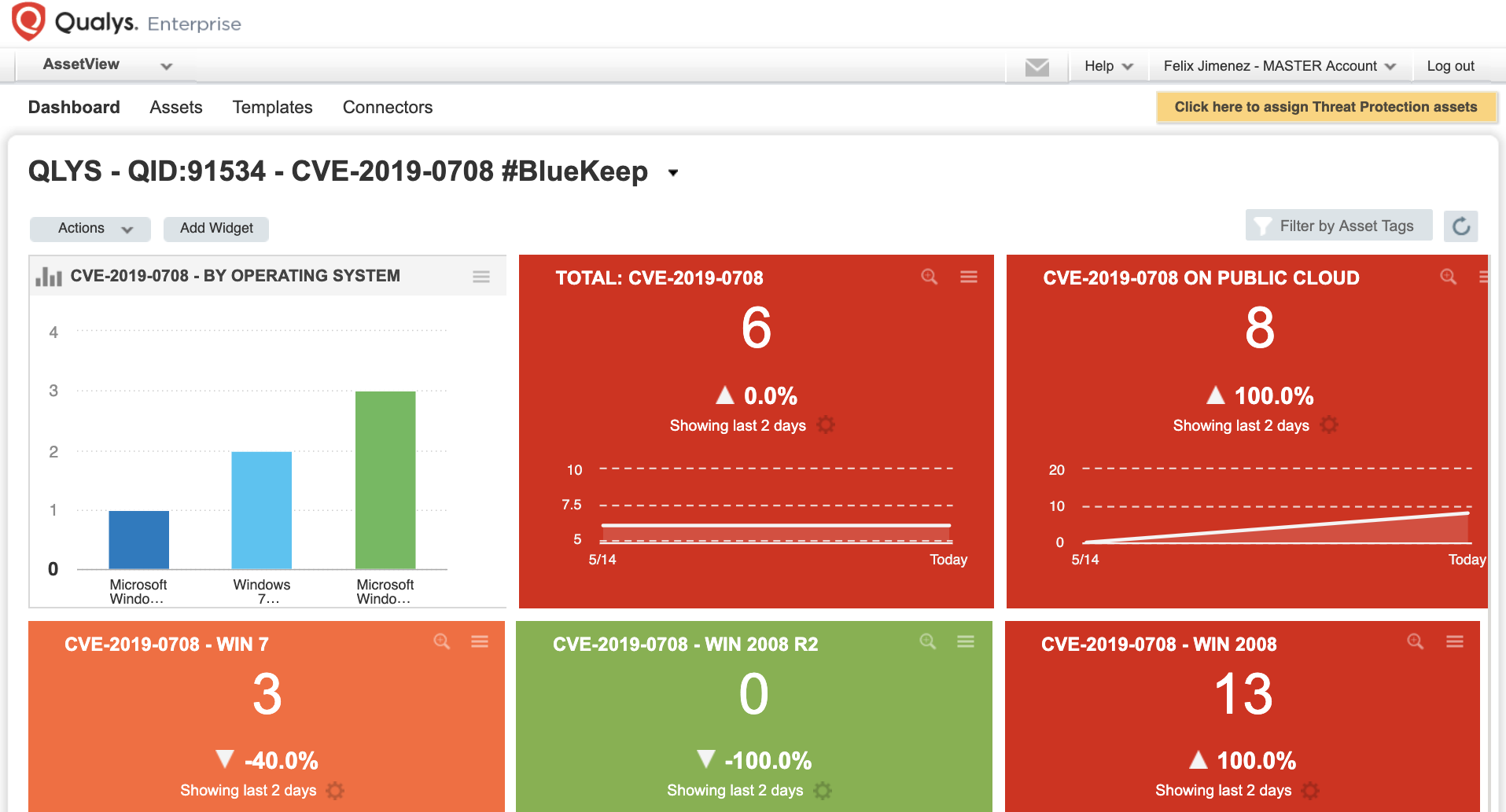
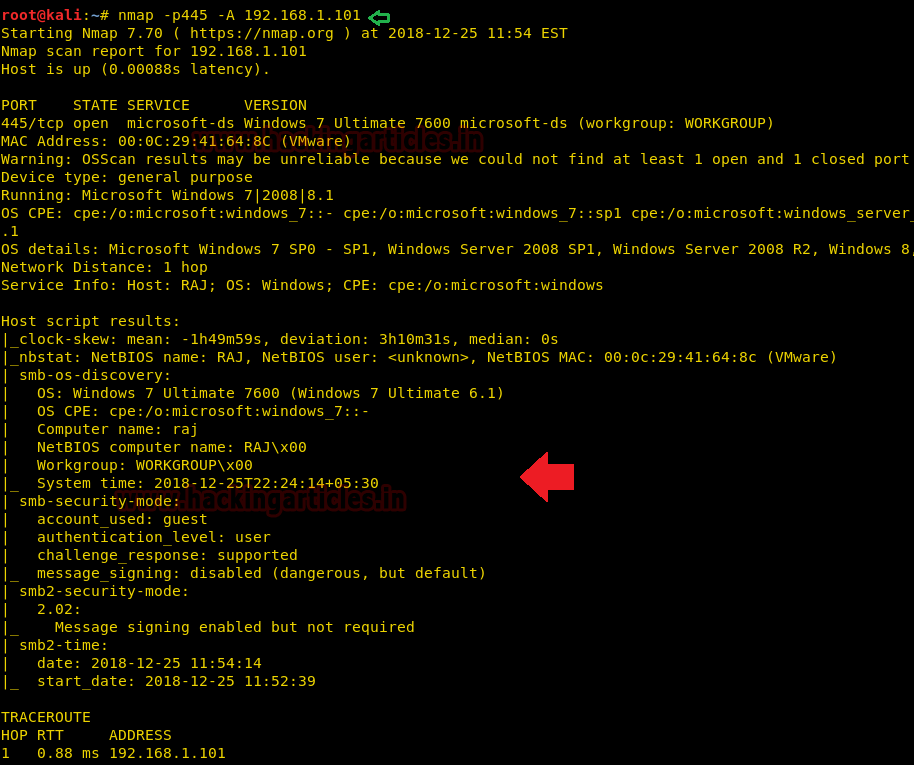
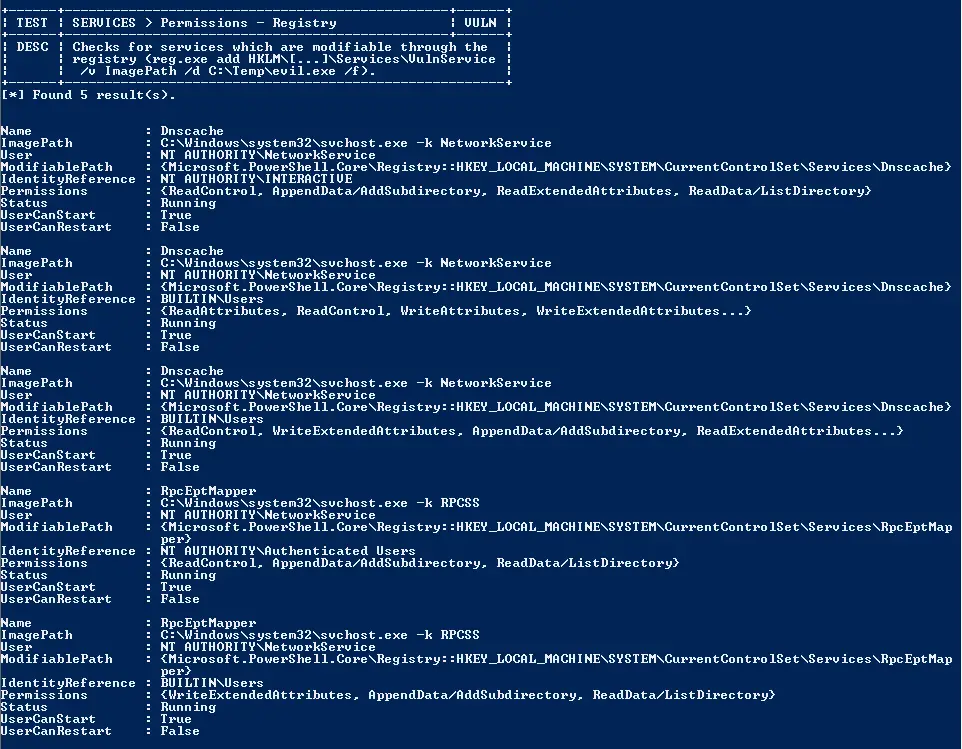
Windows RDP Remote Code Execution Vulnerability (BlueKeep) - How to Detect and Patch | Qualys Security Blog
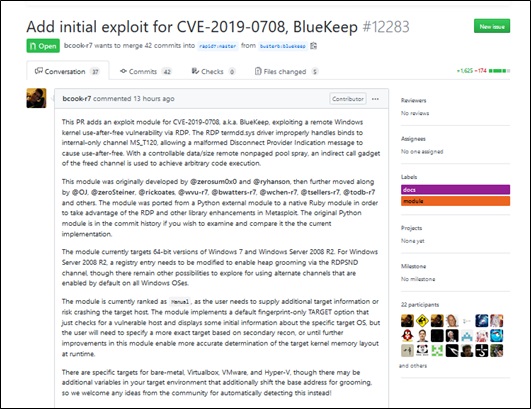
Windows Remote Desktop Services Remote Code Execution Vulnerability (CVE-2019-0708) Exploit Disclosure Threat Alert - NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks.

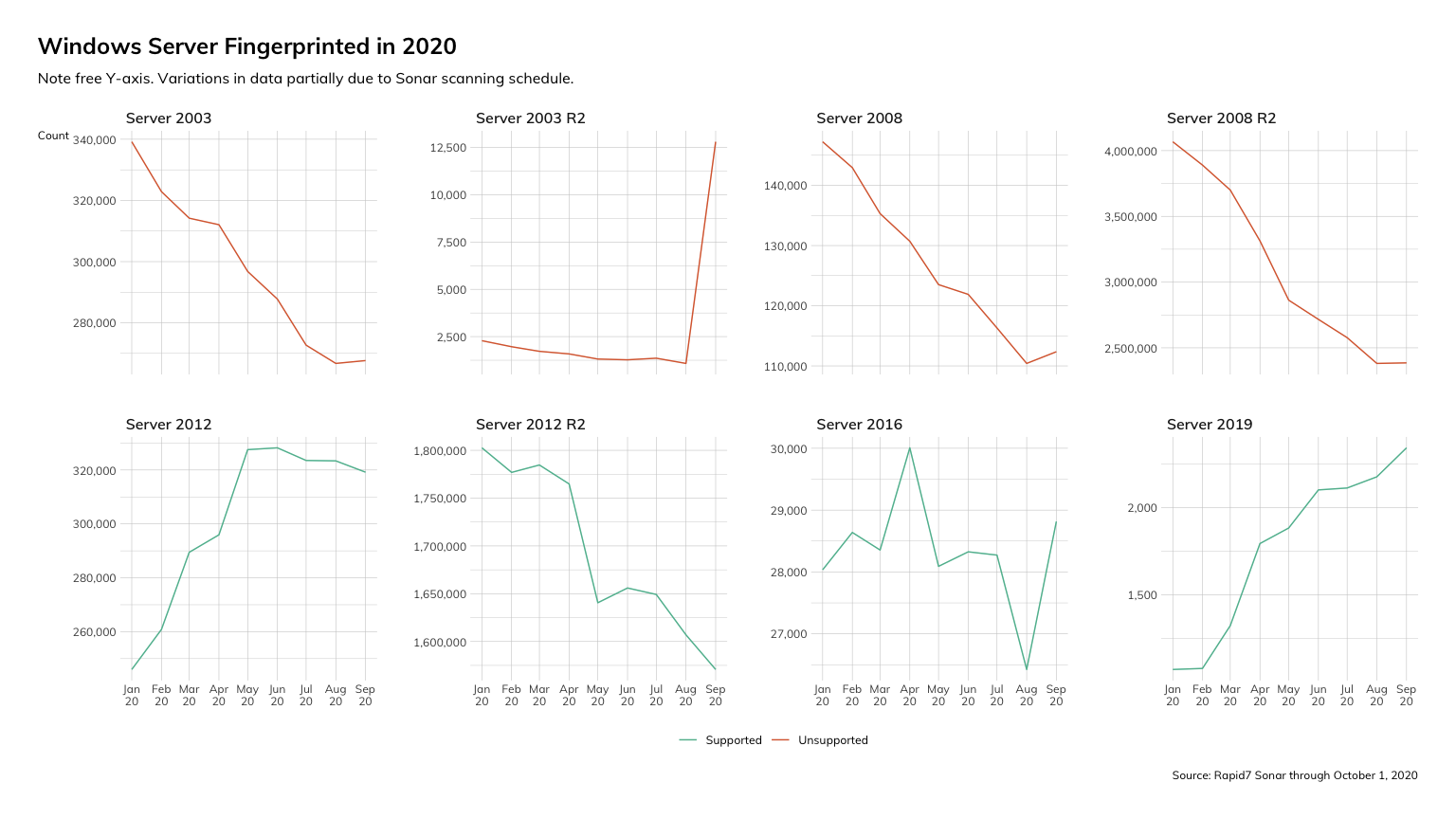
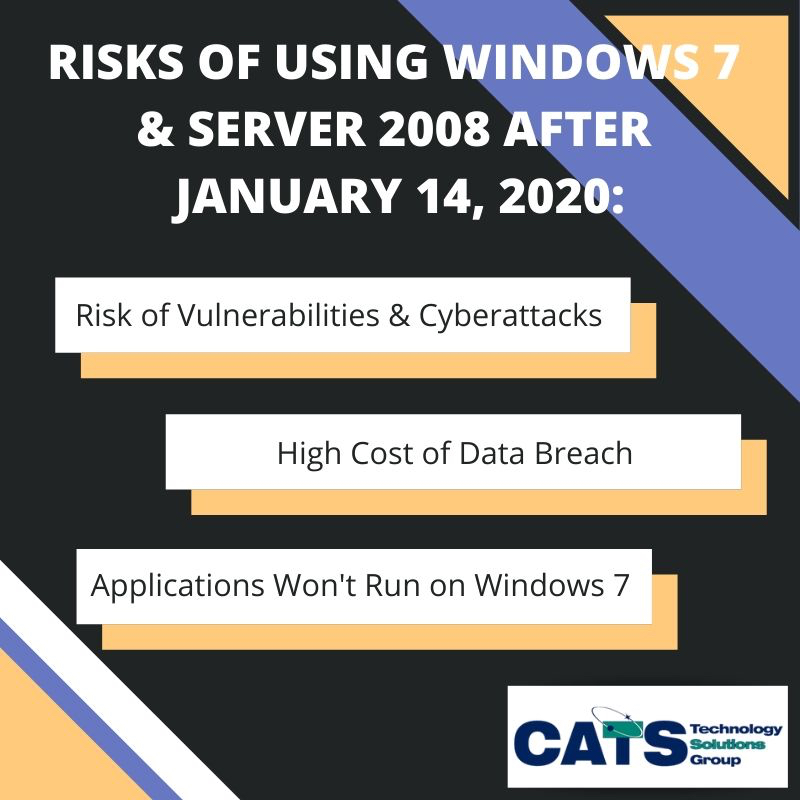
0patch Blog: Micropatching Keeps Windows 7 and Windows Server 2008 R2 Secure After Their End-Of-Support

How to Manually Exploit EternalBlue on Windows Server Using MS17-010 Python Exploit « Null Byte :: WonderHowTo